SIS March 2024: TP-Link Archer AX21 Wifi Router targeting, plus a handful of new CVEs!
The March 2024 Sensor Intelligence Series report highlights a significant surge in scanning activity for the vulnerability CVE-2023-1389 and also notes that most of the scanning traffic originates from two ASNs, suggesting a concentrated effort from specific sources.71Views1like0CommentsThis Month In Security for October, 2022
This Month In Security is a partnership between F5 Security Incident Response Team's AaronJB(Aaron Brailsford), F5 Labs' David Warburton and Tafara Muwandi and F5 DevCentral's AubreyKingF5. This month's news includes some Supply Chain Security, Guidance from CISA and a worrisome UEFI Bootkit.376Views2likes0CommentsF5 Labs Publishes October Update to Sensor Intel Series
F5 Labs just launched the October installment in our growing Sensor Intel Series. The sensors in question come from our data partners Efflux, and allow us to get a sense of what kinds of vulnerabilities attackers are targeting from month to month. In September, the top-targeted vulnerability was CVE-2018-13379, a credential disclosure vulnerability in various versions of two Fortinet SSL VPNs. While nobody likes to see security tools with vulnerabilities, it is a change from the PHP remote code execution and IoT vulnerabilities that have made up the bulk of the targeting traffic over the last several months. We’ve also debuted a new visualization type for all 41 tracked vulnerabilities, making it a little easier to identify vulnerabilities with dramatic changes in targeting volume. At various times in the last nine months, CVE-2017-18368, CVE-2022-22947, and the vulnerabilities CVE-2021-22986 and CVE-2022-1388 (which are indistinguishable without examining headers in the HTTP request) have all shown growth rates at or near three orders of magnitude over a period of six to eight weeks, making them the fastest growing vulnerabilities since we’ve started this project. Stay tuned for the publication of the October SIS in early November. We are always looking for new CVEs to add and new ways to visualize the attack data.1.3KViews2likes0CommentsThe State of the State of Application Exploits in Security Incidents (SoSo Report)
Cybersecurity is always about perspective, and that is doubly true when talking about the rapidly changing field of application security. With The State of the State of Application Exploits in Security Incidents, F5 Labs & Cyentia Institute provide a more complete view of the application security elephant. We examine published industry reports from multiple sources for a better understanding of the frequency and role of application exploits. So, let’s start the clock to learn more about the affectionately named, SoSo Report. Get your copy at F5 Labs727Views0likes0CommentsF5 Labs Report: Cybersecurity Compliance Failures in Financial Services
One important piece of the 2021 Application Protection Report revealed that, of all breaches studied in 2020, the financial sector had the dubious honor of the highest percentage: 17 percent (17%). With breaches, come increased regulatory attention. In 2017, New York’s Department of Financial Services (NYDFS) enacted 23 NYCRR Part 500 regulations, calling out explicit cybersecurity requirements for financial services firms. Since then, three financial services organization that were breached have faced sobering consequences for failing to meet the NYDFS law. This in-depth article looks at each of those breaches in greater detail. Check outCybersecurity Compliance Failures in Financial Serviceson F5 Labs.618Views1like0CommentsSupplement To The 2021 App Protect Report
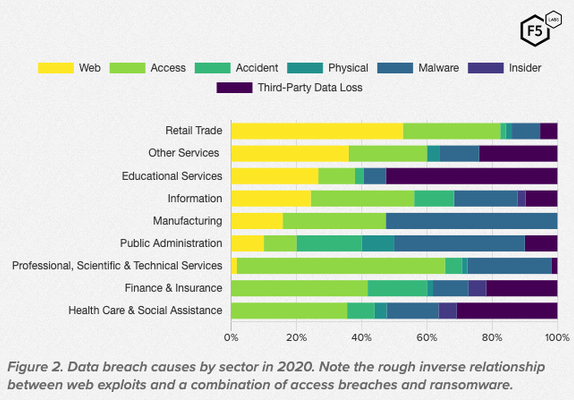
We frequently get requests to break down threats in a specific vertical. So, as a follow up to the F5 Labs, 2021 Application Protection Report (APR), we analyzed and visualized the attack chains of more than 700 data breaches looking for relationships between sectors or industries and the tactics and techniques attackers use against them. This effort produced the F5 Labs 2021 APR Supplement: Sectors and Vectors, where we found that while there are some attack patterns that correspond with sectors, the relationships appear indirect and partial, and counterexamples abound. The overall conclusion is that sectors can be useful for predicting an attack vector, but only in the absence of more precise information such as vulnerabilities or published exploits. This is because the types of data and vulnerabilities in the target environment, which determine an attacker’s approach, are no longer tightly correlated with the nature of the business. Look for more details about your sector (Finance, Education, Health Care, Scientific, Retail, etc) in the F5 Labs, 2021 APR Supplement: Of Sectors and Vectors.207Views2likes0CommentsOf Ransom and Redemption: The 2021 Application Protection Report
The information security professional’s mission has gradually become extraordinarily complex. At times, this mission borders on contradiction. Quite often, responsibility for the various components that form an enterprise environment is spread not only among multiple teams within the enterprise but also among vendors, partners, and service providers. In this 2021 Application Protection Report by F5 Labs, Sander, Ray, Shahnawaz, and Malcom look at the breaches in the past year as a series of attacker techniques, explore the outcomes, and provide some recommendations for controls you can implement in your environment. Some Highlights Two-thirds of API incidents in 2020 were attributable to either no authentication, no authorization, or failed authentication and authorization. In 2020, four sectors—finance/insurance, education, health care, and professional/technical services—experienced a greater number of breaches than retail (the leader in 2018 and 2019), partly driven by the growth in ransomware. The most important controls are privileged account management, network segmentation, restricting web-based content, data backup, and exploit protection (i.e., WAF). DevCentral Connects featuring Sander Vinberg Or, if you prefer, listen to Jason & John talk to Sander, directly, on DevCentral Connects.195Views0likes0CommentsF5 Labs Research: The Rising IoT Threat to the Agriculture Industry
Mike Levin, a guest of F5Labs, describes how cybersecurity best practices are needed for securing our global food supply. Farming is becoming increasingly automated. This means new cybersecurity risks are emerging to stand alongside traditional risks like the weather and pests. Beyond our farmers, technologists and policymakers also need to recognize and address the growing risk.159Views0likes0CommentsThe F5 Labs 2019 Application Protection Report
For the past years, F5 Labs has produced the Application Protection Research Series. First as individual reports and then as a series of episodes released during the year. We have just released the 2019 report final edition, which places years of security trends and patterns into a single long-term picture, to get away from news cycles and hype that only focus on new threats or vulnerabilities that may not even be applicable. This perspective also allows us to see linkages between the different subdomains and foci that make up the complex and porous field we call information security. This new comprehensive report pulls together the various threats, data sources, and patterns in the previous episodes into a unified line of inquiry that began in early 2019, picking up where the 2018 Application Protection Report left off, and concluded in early 2020 with updated data on 2019 breaches and architectural risk. One of the underlying themes for the 2019 series has been that changes in the ways that we design, build, and deploy applications have been drivers for risk. From third-party services driving the rise of an injection attack known as formjacking, to a growing list of seemingly avoidable API breaches, to the prevalence of platforms running on languages with old and documented flaws, there has been a good deal of goalpost movement for defenders. The implication is that many of the people who are making decisions with significant ramifications for security—system owners, application architects, DevOps teams—are generally placing other priorities ahead of security. Based on the acceleration of trends in 2019 that we identified from 2018, it seems that this tension will characterize the next few years of the security arms race. Our top conclusions in this report include: Access attacks predominant except for retail Retail breaches increasingly dominated by formjacking Breach modes driven more by application architecture than by traditional sector Get the Full report here https://www.f5.com/labs/articles/threat-intelligence/2019-application-protection-report Executive Summary https://www.f5.com/labs/articles/threat-intelligence/application-protection-research-series-executive-summary341Views1like0CommentsF5 Labs 2019 TLS Telemetry Report Summary
Encryption standards are constantly evolving, so it is important to stay up to date with best practices. The 2019 F5 Labs TLS Telemetry Summary Report by David Warburton with additional contributions from Remi Cohen and Debbie Walkowski expands the scope of our research to bring you deeper insights into how encryption on the web is constantly evolving. We look into which ciphers and SSL/TLS versions are being used to secure the Internet’s top websites and, for the first time, examine the use of digital certificates on the web and look at supporting protocols (such as DNS) and application layer headers. On average, almost 86% of all page loads over the web are now encrypted with HTTPS. This is a win for consumer privacy and security, but it’s also posing a problem for those scanning web traffic. In our research we found that 71% of phishing sites in July 2019 were using secure HTTPS connections with valid digital certificates. This means we have to stop training users to “look for the HTTPS at the start of the address” since attackers are using deceptive URLs to emulate secure connections for their phishing and malware sites. Read our report for details and recommendations on how to bolster your HTTPS connections.350Views1like0Comments