Kerberos SSO to IIS Web Application
 Nimbostratus
Nimbostratus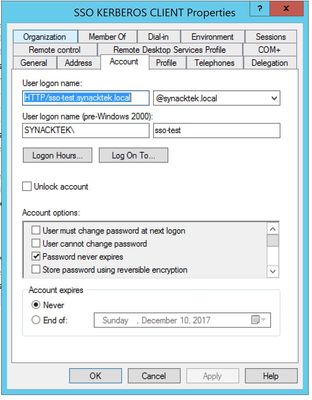
I would suggest that you do a packet capture and look if the client is fetching a kerberos token and presents it to the APM
 Nimbostratus
NimbostratusI am using IE as the browser, I do have the site added as intranet and enable integrated windows authentication is checked.
I do not see any kerberos traffic in my pcap but I do see what appears to be NTLM.
 Nimbostratus
NimbostratusOk made a bunch of progress this evening and I have the aaa "client" side working. I verified that I am getting a kerberos ticket back from AD and then presenting it to APM where it looks like it is decrypting it no problem (I have a green light session now).
Moving on to the SSO side I am having an issue here still that I cannot figure out. This is what I see in the log now:
I will doublecheck my sso config to be sure and might see if I can get a packet capture of the server side process.
-Bill
 Nimbostratus
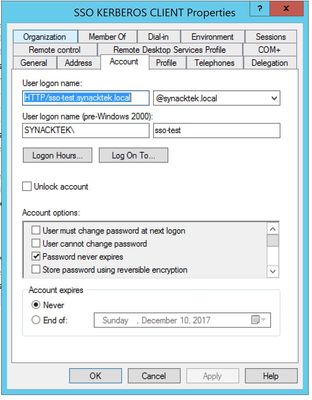
NimbostratusDoes the user logon name in AD need to match the reverse DNS of the target IIS pool member?
In other words I have this for the logon name:
My forward and reverse DNS of the pool member IIS server is this:
192.168.210.55 is my pool member of the virtual server.
And my SSO configuration on the F5 reflects this user logon account:
The APM log for sso always shows this:
I do not know why it keeps saying matching credential not found here.
Oh, and if I go against the URL of the internal server directly from a domain machine it does automatically log me on and connect me so I think the IIS side is ok.
-Bill
 Cumulonimbus
CumulonimbusThe default SPN used by APM is based on the reverse dns
If you want to use SPN based on Host value, change SPN pattern to
HTTP/%h
 Nimbostratus
NimbostratusThank you, I may try this. But the reverse dns is what I have configured as the account so that "should" be working. Something with AD or the delegation seems to be wrong but everything I look at appears correct.
-Bill
 MVP
MVPthat failed to get ticket can't be ok, you have to correct setup there?
 Nimbostratus
NimbostratusThat's the issue, I am pretty sure (unless I am way off here) that my F5 APM (aaa/sso) config is good. There is something going on in the AD world that I don't understand and am really having a hard time figuring out how to troubleshoot. When I do a packet capture on the F5, I don't see any kerberos traffic being sent toward the domain controller for SSO.
-Bill
 MVP
MVPwhat are you filtering on for the packet capture? might be it goes to a system you don't expect.